Stephen Kost's E-Business Suite Security Blog
Log4j Vulnerabilities Impact On Oracle E-Business Suite - Updated Information
Multiple significant security vulnerabilities (CVE-2021-44228, CVE-2021-45046, and CVE-2021-4104) have been disclosed and patched in the popular Java logging library Apache Log4j. This library is installed in Oracle E-Business Suite (EBS) environments and these vulnerabilities may be exploitable in your environment depending on Oracle EBS version, Oracle EBS patches applied, and customizations or third-party products.
On December 15th, Oracle has changed the remediation with the disclosure of the most recent Log4j security vulnerability (CVE-2021-45046) as the initial recommended fix was not complete.
Integrigy has completed a detailed analysis on the impact of these Log4j security vulnerabilities on Oracle E-Business Suite and you can access this analysis here -
Integrigy Log4j Vulnerabilities Impact on Oracle E-Business Suite Analysis
Integrigy's products AppDefend and AppSentry does not use the Log4j library, therefore, are not vulnerable to this security bug.
Please let us know if you have any questions regarding this security vulnerability at info@integrigy.com.
Upcoming Webinar: Oracle Database 21c New Security Features
Thursday, January 28, 2021 - 2:00 pm to 3:00 pm EST
Oracle Database 21c has been released and is the latest innovation release of the Oracle Database. A number of new security features are included with this release and should be adopted when creating new databases or upgrading existing databases. This educational webinar will review the new security features and changes in security for this database release. Key new security features are blockchain table, gradual database password rollover, mandatory case sensitive passwords, and Unified Auditing enhancements.
Upcoming Webinar: Oracle E-Business Suite Security for Auditors
Oracle E-Business Suite Security for Auditors
Thursday, December 17, 2020 - 2:00 pm to 3:00 pm EST
Auditors are trained to understand the financial aspects and the end user functionality of Oracle E-Business Suite. However, most auditors have not been trained in the security features and technical aspects of Oracle E-Business Suite. This education webinar will dive into the key security features within Oracle E-Business Suite. Key configuration settings, protecting sensitive data, concerns and risks with user privileges, and compliance issues related to SOX will be discussed and how to audit these areas.
Upcoming Webinar: Is Your Sensitive Data Playing Hide and Seek with You?
Is Your Sensitive Data Playing Hide and Seek with You?
Thursday, December 12, 2019 - 2:00 pm EST
Your Oracle databases and ERP applications may contain sensitive personal data like Social Security numbers, credit card numbers, addresses, date of births, and salary information. Understanding in what tables and columns sensitive data resides is critical in protecting the data and ensure compliance with regulations like GDPR, PCI, and the new California Consumer Privacy Act (CCPA). However, sensitive data is like a weed and can spread quickly if not properly managed. The challenge is how to effectively and continuously find sensitive data, especially in extremely large databases and data warehouses. This educational webinar will discuss methodologies and tools to find sensitive such as by searching column names, crawling the database table by table, and performing data qualification to eliminate false positives. Other locations where sensitive data might reside such as trace files, dynamic views (e.g., V$SQL_BIND_DATA), and materialized views will be reviewed.
CVE-2019-2638, CVE-2019-2633, Oracle Payday Vulnerabilities - AppDefend Protection
Two Oracle E-Business Suite security vulnerabilities (CVE-2019-2638, CVE-2019-2633) fixed in April 2019 Oracle Critical Patch Update (CPU) have been recently publicized. These vulnerabilities allow an attacker to execute arbitrary SQL statements in the Oracle E-Business Suite data that can result in complete compromise of the environment including fraudulent transactions, changing of bank accounts, and circumvention of application security controls. Integrigy’s AppDefend, the application firewall for Oracle E-Business Suite, is the only solution that provides virtual patching for and proactive defense against these vulnerabilities.
These two vulnerabilities are in the Oracle E-Business Suite (EBS) TCF Server, which provides services to the professional Forms interface for a limited set of Forms. TCF Server is implemented and enabled in all versions of Oracle E-Business Suite including 11i, 12.0, 12.1, and 12.2. It can not be disabled without a customization to Oracle EBS.
TCF Server is a servlet running as part of the standard Oracle EBS web application server and communicates using HTTP or HTTPS between the Forms Java client and the web application server. For R12, the servlet is available at the URL /OA_HTML/AppsTCFServer. It uses a proprietary application-level protocol to communicate between the Forms client and server.
The risk is that unlike most Oracle EBS SQL injection vulnerabilities that only allow for fragments of SQL statements to be appended to standard Oracle EBS SQL statements being executed, these security bugs allow execution of complete SQL statements as the Oracle EBS APPS database account. When evaluating the risk of these vulnerabilities in your environment, it is important to differentiate between external access to the Oracle EBS environment through the Internet when modules like iSupplier, iStore, and iRecruitment are being used and internal access from only your internal network. The risk from external access is critical and should be immediately addressed. The internal risk is still high and dependent on the security posture of your internal network. It is important to realize that non-Oracle EBS aware web application firewalls, database security tools, and other network security products will not provide any protection from successful exploitation of these vulnerabilities.
Integrigy AppDefend is the only solution that provides virtual patching for and proactive defense against these TCF Server vulnerabilities as well other Oracle EBS security vulnerabilities. Integrigy recognized the potential issues with TCF Server and even the first release of AppDefend for R12 in 2007 blocked external access to the TCF Server by default.
AppDefend provides multiple layers of protection against TCF Server vulnerabilities as follows -
- Blocks all access to TCF Server externally (since 2007).
- Enforces Oracle EBS access control for TCF Server allowing only authorized EBS users to access to the TCF Server (since 2018).
- Whitelists the functions accessible through TCF Server (since 2018).
- Blocks specific vulnerabilities in TCF Server (2018, 2019).
- Advanced SQL injection protection optimized specifically for Oracle EBS will detect and block most of the SQL statements used in TCF Server and other 0-day attacks. (since 2007).
If you do not have AppDefend, applying the latest Oracle Critical Patch Update for Oracle EBS will remediate these specific vulnerabilities and for external sites it is critical that the Oracle EBS URL Firewall is implemented as documented in Appendix E of My Oracle Support Note ID 380490.1. However, these solutions will not protect you prior to applying the security patches or against future TCF Server vulnerabilities and other Oracle EBS 0-day attacks.
Please let us know if you have any questions regarding the latest Oracle EBS security vulnerabilities at info@integrigy.com.
Integrigy at COLLABORATE 19 - Oracle E-Business Suite Security, Database Security, PeopleSoft Security
Heading to COLLABORATE 19? For the 12th consecutive year, Integrigy will be presenting on Oracle E-Business security, Oracle Database security, and PeopleSoft security. If you will be attending, be sure to schedule in one or more of our presentations.
Oracle E-Business Suite Security
Top 10 Oracle E-Business Suite Security Risks Tuesday April 9 - 10:30 AM-11:30 AM - GH 4th FL Republic C
How to Close the Window between Oracle CPU Security Release and Deployment Tuesday April 9 - 4:30 PM-5:30 PM - GH 4th FL Republic C
GDPR Compliance and the Oracle E-Business Suite Revisited Thursday April 11 - 9:15 AM-10:15 AM - GH 4th FL Seguin B
Oracle Database Security
An Introduction to Oracle Database Security Wednesday April 10 - 8:00 AM-9:00 AM - CC 2nd FL 221A
Hacking an Oracle Database and How to Prevent It Wednesday April 10 - 2:00 PM-3:00 PM - CC 2nd FL 205
Oracle Database Multitenant Security Explained Thursday April 11 - 8:00 AM-9:00 AM - CC 2nd FL 206B
PeopleSoft Security
Top 10 Security Risks in a PeopleSoft Environment Monday April 8 - 4:30 PM-5:30 PM - GH 3rd FL Bonham D
Oracle Critical Patch Update July 2018 Oracle PeopleSoft Analysis and Impact
As with almost all previous Oracle E-Business Suite Critical Patch Updates (CPU), the July 2018 quarterly patch is significant and high-risk for PeopleSoft applications. Despite the publicity, marketing, or naming of specific vulnerabilities, this quarter is no different than previous quarters in terms of risk and prioritization within your organization.
For this quarter, there are 15 security vulnerabilities patches in PeopleSoft applications and PeopleTools --
10 - PeopleTools
2 - PeopleSoft Financials
2 - PeopleSoft HCM
1 - PeopleSoft Campus Solutions
11 of the 15 security vulnerabilities are remotely exploitable without authentication, therefore, an attacker can exploit the PeopleSoft without any credentials. For this quarter, there are 7 cross-site scripting vulnerabilities, 3 vulnerabilities in third-party libraries used in PeopleSoft, and 5 other types of vulnerabilities.
10 cross-site scripting (XSS) vulnerabilities and 4 other types of vulnerabilities fixed. Most important is that 13 of the 14 vulnerabilities are remotely exploitable without authentication.
For PeopleTools, only 8.55 and 8.56 are supported. Previous versions of PeopleTools must be upgraded in order to apply the security patches.
Tuxedo
Another vulnerability for Tuxedo JOLT (CVE-2018-3007) is fixed in this CPU, therefore, Tuxedo must also be patched. Configuration changes must be made to the Tuxedo server in order to limit connections to both JSH and WSH in order to reduce the risk of security vulnerabilities.
WebLogic
A number of vulnerabilities in WebLogic are fixed in this CPU including a vulnerability accessible via the T3 protocol. In addition to applying the appropriate WebLogic security patch, the WebLogic should be configured to only allow access to the HTTPS protocol.
Oracle Database
For the July 2018 CPU, only 11.2.0.4 and 12.1.0.2 are supported for security patches. For the database, there is a OJVM security patch, so either the combo patch must be applied or a separate OJVM patch must be applied to correct the vulnerability in the Java Virtual Machine (JVM) in the database which is used by PeopleSoft.
July 2018 Recommendations
As with almost all Critical Patch Updates, the security vulnerabilities fixes are significant and high-risk. Corrective action should be taken immediately for all PeopleSoft environments. The most at risk implementations are Internet facing environments and Integrigy rates this CPU as high risk due to the large number of cross-site scripting (XSS) vulnerabilities that can be remotely exploited without authentication. These implementations should apply the CPU as soon as possible or use a virtual patching solution such as AppDefend.
Most PeopleSoft environments do not apply the CPU security patch in a timely manner and are vulnerable to full compromise of the application through exploitation of multiple vulnerabilities. If the CPU cannot be applied quickly, the only effective alternative is the use of Integrigy's AppDefend, an application firewall for the Oracle PeopleSoft. AppDefend provides virtual patching and can effectively replace patching of PeopleSoft web security vulnerabilities.
CVEs referenced: CVE-2017-5645, CVE-2018-1275, CVE-2018-2990, CVE-2018-2977, CVE-2018-0739, CVE-2018-2951, CVE-2018-3068, CVE-2018-2929, CVE-2018-2919, CVE-2018-2985, CVE-2018-2986, CVE-2018-3016, CVE-2018-3072, CVE-2018-2970, CVE-2018-3076
Oracle Critical Patch Update July 2018 Oracle E-Business Suite Analysis and Impact
As with almost all previous Oracle E-Business Suite Critical Patch Updates (CPU), the July 2018 quarterly patch is significant and high-risk. 51 of the past 55 quarterly patches are significant and high-risk as they fix one or more SQL injection vulnerabilities or other damaging security vulnerabilities in the web application of Oracle E-Business Suite. Despite the publicity, marketing, or naming of specific vulnerabilities, this quarter is no different than previous quarters in terms of risk and prioritization within your organization.
For this quarter, there are 10 cross-site scripting (XSS) vulnerabilities and 4 other types of vulnerabilities fixed. Most important is that 13 of the 14 vulnerabilities are remotely exploitable without authentication.
Externally facing Oracle E-Business Suite environments (DMZ) running iStore should take immediate action to mitigate the three vulnerabilities impacting iStore. These web pages are allowed by the URL Firewall if the iStore module is enabled. Two of the three are cross-site scripting (XSS) vulnerabilities, which requires interaction with the end-user such as clicking a link but allows for the attacker to hijack the end-users session.
July 2018 Recommendations
As with almost all Critical Patch Updates, the security vulnerabilities fixes are significant and high-risk. Corrective action should be taken immediately for all Oracle E-Business Suite environments. The most at risk implementations are those running Internet facing self-service modules (iStore for this CPU) and Integrigy rates this CPU as high risk due to the large number of cross-site scripting (XSS) vulnerabilities that can be remotely exploited without authentication. These implementations should (1) apply the CPU as soon as possible or use a virtual patching solution such as AppDefend and (2) ensure the DMZ is properly configured according to the EBS specific instructions and the EBS URL Firewall is enabled and optimized.
Most Oracle E-Business Suite environments do not apply the CPU security patch in a timely manner and are vulnerable to full compromise of the application through exploitation of multiple vulnerabilities. If the CPU cannot be applied quickly, the only effective alternative is the use of Integrigy's AppDefend, an application firewall for the Oracle E-Business Suite. AppDefend provides virtual patching and can effectively replace patching of EBS web security vulnerabilities.
Oracle E-Business Suite 12.1 and 12.2 Patching
For 12.2, there are no significant changes from previous CPUs and 12.2.3 along with R12.AD.C.DELTA.10 and R12.TXK.C.DELTA.10 roll-up patches is the minimum baseline. In addition to the cumulative EBS security patch, the July 2018 WebLogic 10.3.6 PSU must be applied (PSU 10.3.6.0.180717 - Patch 27919965).
For 12.1, there are no significant changes from the previous CPUs and the major requirement is the Oracle Application Server must be upgraded to 10.1.3.5. No security patches are required for the Oracle Application Server.
Only 12.1.0.2 and 11.2.0.4 versions of the Oracle Database are supported and the database must be upgraded in order to apply this quarter's database security patch if it has not already been upgraded. For the database there is a OJVM security patch, so either the combo patch must be applied or a separate OJVM patch must be applied to correct the vulnerability in the Java Virtual Machine (JVM) in the database which is used by Oracle E-Business Suite.
Oracle E-Business Suite 12.0
CPU support for Oracle E-Business Suite 12.0 ended January 2015 and there are no security fixes for this release. Integrigy’s initial analysis of the CPU shows all 14 vulnerabilities are exploitable in 12.0. In order to protect your application environment, the Integrigy AppDefend application firewall for Oracle E-Business Suite provides virtual patching for all these exploitable web security vulnerabilities.
Oracle E-Business Suite 11i
As of April 2016, the 11i CPU patches are only available for Oracle customers with Tier 1 Support. Integrigy’s analysis of the July 2018 CPU shows at least 6 of the 14 vulnerabilities are also exploitable in 11i. 11i environments without Tier 1 Support should implement a web application firewall and virtual patching for Oracle E-Business Suite in order to remediate the large number of unpatched security vulnerabilities. As of July 2018, an unsupported Oracle E-Business Suite 11i environment will have approximately 200 unpatched vulnerabilities – a number of which are high-risk SQL injection security bugs.
11i Tier 1 Support has been extended through December 2018, thus October 2018 will be the final CPU for Oracle E-Business Suite 11i. At this time it is unclear if Oracle will again extend support for another year, therefore, organizations should plan that support will not be extended and being to take corrective action to ensure their environments are properly secured.
CVEs Referenced: CVE-2018-2993, CVE-2018-3017, CVE-2018-2995, CVE-2018-3018, CVE-2018-3008, CVE-2018-2953, CVE-2018-2997, CVE-2018-2991, CVE-2018-3012, CVE-2018-2996, CVE-2018-2954, CVE-2018-2988, CVE-2018-2934, CVE-2018-2994
CVE-2017-10151 Oracle Identity Manager Vulnerability
Oracle has released an out-of-cycle security advisory (CVE-2017-10151) for a vulnerability affecting Oracle Identity Manager. This vulnerability has a CVSS 3.0 base score of 10 out of 10. Oracle Identity Manager is the identity governance component within the Oracle Identity Management solution. All supported versions of Identity Manager are impacted from 11.1.1.7 to 12.2.1.3.0. Most likely 11.1.1.1 through 11.1.1.6 are also vulnerable. Previous Identity Manager versions (10g and 9.x) that are not based on Oracle WebLogic are probably not vulnerable.
The vulnerability is that the Oracle Identity Manager system user account (OIMINTERNAL) can be accessed using the default password through the Oracle WebLogic server. As this is a highly privileged user, the entire Identity Manager environment can be completely compromised via an unauthenticated network attack.
The work-around is to change the OIMINTERNAL user password to a random string in the WebLogic administration console under Domain -> Security Realms. A patch will be available in the future to automatically change the password. See My Oracle Support Note "Oracle Security Alert CVE-2017-10151 Patch Availability Document for Oracle Identity Manager (Doc ID 2322316.1)" for more information.
As Oracle released an out-of-cycle security advisory, either detailed information regarding the vulnerability has been released or will soon be released, or Oracle has been informed the vulnerability is being actively exploited.
Oracle Critical Patch Update October 2017 Oracle E-Business Suite Analysis and Impact
As with almost all previous Oracle E-Business Suite Critical Patch Updates (CPU), the October 2017 quarterly patch is significant and high-risk. 47 of the past 52 quarterly patches are significant and high-risk as they fix one or more SQL injection vulnerabilities or other damaging security vulnerabilities in the web application of Oracle E-Business Suite. Despite the publicity, marketing, or naming of specific vulnerabilities, this quarter is no different than previous quarters in terms of risk and prioritization within your organization.
For this quarter, there are 3 SQL injection vulnerabilities, 16 cross-site scripting (XSS) vulnerabilities, 3 information disclosures, and 4 other types of vulnerabilities fixed. Most important is that 25 of the 26 vulnerabilities are remotely exploitable without authentication.
Externally facing Oracle E-Business Suite environments (DMZ) running iStore or iSupport should take immediate action to mitigate the two vulnerabilities impacting iStore and four vulnerabilities impacting iSupport (and Knowledge Management). These web pages are allowed by the URL Firewall if the iStore or iSupport modules are enabled. All six are cross-site scripting (XSS) vulnerabilities, which requires interaction with the end-user such as clicking a link but allows for the attacker to hijack the end-users session.
October 2017 Recommendations
As with almost all Critical Patch Updates, the security vulnerabilities fixes are significant and high-risk. Corrective action should be taken immediately for all Oracle E-Business Suite environments. The most at risk implementations are those running Internet facing self-service modules (i.e., iStore, iSupplier, iSupport, etc.) and Integrigy rates this CPU as a critical risk due to the number of SQL injection vulnerabilities that can be remotely exploited without authentication. These implementations should (1) apply the CPU as soon as possible or use a virtual patching solution such as AppDefend and (2) ensure the DMZ is properly configured according to the EBS specific instructions and the EBS URL Firewall is enabled and optimized.
Most Oracle E-Business Suite environments do not apply the CPU security patch in a timely manner and are vulnerable to full compromise of the application through exploitation of multiple vulnerabilities. If the CPU cannot be applied quickly, the only effective alternative is the use of Integrigy's AppDefend, an application firewall for the Oracle E-Business Suite. AppDefend provides virtual patching and can effectively replace patching of EBS web security vulnerabilities.
Oracle E-Business Suite 11i
As of April 2016, the 11i CPU patches are only available for Oracle customers with Tier 1 Support. Integrigy’s analysis of the October 2017 CPU shows at least 18 of the 26 vulnerabilities are also exploitable in 11i. 11i environments without Tier 1 Support should implement a web application firewall and virtual patching for Oracle E-Business in order to remediate large number of unpatched security vulnerabilities. As of October 2017, an unsupported Oracle E-Business Suite 11i environment will have approximately 170 unpatched vulnerabilities – a number of which are high-risk SQL injection security bugs.
11i Tier 1 Support has been extended through December 2018, thus October 2018 will be the final CPU for Oracle E-Business Suite 11i.
Oracle E-Business Suite 12.0
CPU support for Oracle E-Business Suite 12.0 ended January 2015 and there are no security fixes for this release. Integrigy’s analysis of the CPU shows at least 22 of the 26 vulnerabilities are exploitable in 12.0. In order to protect your application environment, the Integrigy AppDefend application firewall for Oracle E-Business Suite provides virtual patching for all these exploitable web security vulnerabilities.
Integrigy at Oracle Open World 2017
Integrigy will be presenting again this year on database security at Oracle Open World 2017 (San Francisco, October 1-5). If you will be attending Open World, please join us for this informative session on database security.
The Thrifty DBA Does Database Security
Sunday, Oct 01, 10:45 a.m. - 11:30 a.m. | Moscone South - Room 159
Stephen Kost, Founder and CTO, Integrigy Corporation
Properly securing an Oracle Database requires significant effort and often expensive security add-on products. The Thrifty DBA likes having secure databases, but doesn’t like to spend money on expensive security products when equivalent zero or low-cost solutions are available. In this session discover thrifty yet effective security solutions to solve auditing, encryption, virtual private database, and authentication challenges.
Integrated Cloud Platform: Database, Identity and Security
Code: SUN5690
Please let us know if you would like to meet while at Open World to discuss Oracle Database or Oracle E-Business Suite security.
SCAP OVAL SQL57_TEST Example For Oracle E-Business Suite
Last week I posted a blog introducing SCAP and OVAL. Here is a quick follow-up with a link to a sql57_test example using the Oracle E-Business Suite - it will suffice for any Oracle database.
A great book to read first on SCAP titled ‘Security Automation Essentials’ for $15 on Amazon is a must read: https://www.amazon.com/Security-Automation-Essentials-Streamlined-Communication/dp/0071772510. I would highly recommend this book to anyone interested in SCAP and much thanks to Witte, Cook, Kerr and Shaffer for writing it.
If you have any questions, please contact us at info@integrigy.com
-Michael Miller, CISSP-ISSMP, CCSP, CCSK
ReferencesSTIGS, SCAP, OVAL, Oracle Databases and ERP Security
Last week’s unprecedented ransomware cyber attacks (http://preview.tinyurl.com/lhjfjgk) caught me working through some research on security automation. The cyber attacks evidently were attributed to an unpatched Windows XP vulnerability. When challenged with securing 1,000s of assets such as all the Windows desktops and Linux servers in an organization, automation quickly becomes a requirement.
Automation is increasingly coming up in our client conversations about how to secure the technology ‘stack’ supporting large ERP implementations such as the Oracle E-Business Suite, PeopleSoft, and SAP. For example, how do you from a security professional perspective, communicate an objective risk assessment comprehensive of both the secure baseline configuration (control adherence/violation) and security patch levels (patch/unpatched CVEs) for the Linux operating systems, virtualization software, web server, database and the ERP application itself? Without automation, it is not feasible to promptly produce risk-based assessments of the complete technology stack and to produce results that are readily expressed in a common risk measurement (e.g. CVE) not requiring deep subject matter expertise.
Automation, however, can only be considered after requirements have been defined. I have long used Security Technical Implementation Guides (STIGs) in both my research and work with clients to define security requirements. STIGs are secure configuration standards developed by the US Department of Defense for products such as the Oracle RDBMS and are freely available (http://iase.disa.mil/stigs/Pages/index.aspx). While most clients do not need their databases hardened to military specifications, STIGs are an invaluable source of security best practice thinking.
STIGs (security checklists) are only available in xml format – not PDF files. DISA does provide a utility to view and work with STIGs (http://iase.disa.mil/stigs/Pages/stig-viewing-guidance.aspx) which allows you to manually execute the checklist, record your findings and then export the results. See this YouTube (https://www.youtube.com/watch?v=-h_lj5sWo4A) posting for a great summary of the STIG Viewer and how to use it.
Security Content Automation Protocol (SCAP)To answer the question of how do you automate STIG and/or security checklists, again the Department of Defense has thought through the challenges and has created the Security Content Automation Protocol (SCAP).
SCAP is a multi-purpose framework to automate the security scanning of configurations, vulnerabilities, patch checking and compliance. SCAP content is developed by the National Institute of Standards and Technologies (NIST) and the components are described in the table below. The key point is that SCAP security content (checklists) is free and that the SCAP content scanning tools are available both in open source and commercial options.
SCAP Component
Description eXtensible Checklist Configuration Description Format (XCCDF) XML-based language for specifying checklists and reporting the results of checklist evaluations. Open Vulnerability and Assessment Language (OVAL) XML-based language for specifying test procedures to detect machine state Common Vulnerabilities and Exposures (CVE) Nomenclature and dictionary of security-related security flaws Common Configuration Enumeration (CCE) Nomenclature and dictionary of software security configuration issues Common Vulnerability Scoring System (CVSS) Methodology for measuring the relative security of software flaws Open Checklist Interactive Language (OCIL) XML-based language for specifying security checks that require human interaction or that otherwise cannot be bundled by OVAL Asset Reporting Format (ARF) Standardized data model for sharing information about assets to facilitate the reporting, correlating, and fusing of asset security information. OpenSCAPThere are many tools, Integrigy’s AppSentry included (https://www.integrigy.com/products/appsentry), that will perform a STIG scan of an Oracle database. The question I was researching this week, is could I use a single SCAP tool to automate the scanning of both the Linux server and the database as well as possibly ERP configurations for PeopleSoft and/or the Oracle E-Business Suite – can could I possibly do this with open source software?
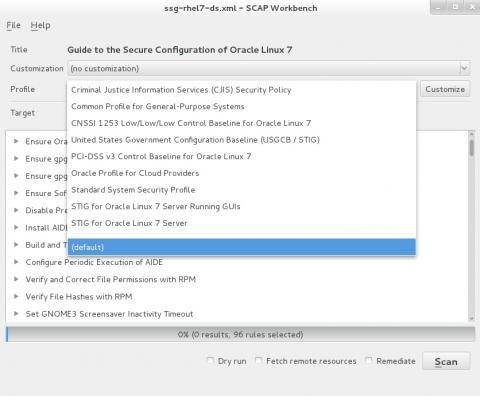
The first tool I considered was OpenSCAP (https://www.open-scap.org/). This open source tool is easy to install either on your laptop or Linux database server and has remote scanning capabilities. The example below shows the capabilities of the GUI tool ‘SCAP Workbench’ and the freely available content that is installed by default for scanning a Linux server.
This exercise quickly confirmed that there is a great deal of security automation available for Linux system security configurations. Here, though, is where I hit a wall: could OpenSCAP work with Oracle databases? While the SCAP standards clearly showed support for scanning SQL database configurations using OVAL’s SQL probes (e.g. sql_test, sql57_test etc…), I may be corrected, but the standard build of OpenSCAP do not appear to include the SQL probes.
JOVAL
To obtain the SQL probes for SCAP scanning of database configurations, after some research, I obtained an evaluation copy of Joval Professional (http://jovalcm.com/). Joval describes themselves as allowing you to Scan anything from anywhere and to allow continuous configuration assessments for developers, enterprises, content authors and security professionals.
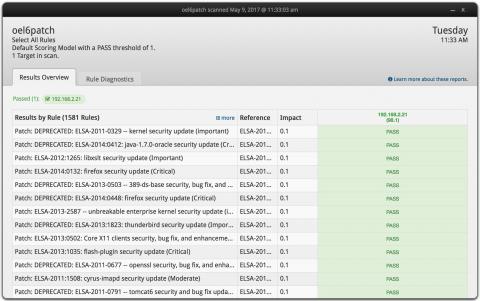
The installation of Joval Professional was quick and I was able to scan my laptop and remotely scan the remote Oracle Linux server without issues. The screen shot below shows the results of the remote scan of the Linux server running the Oracle RDBMS.
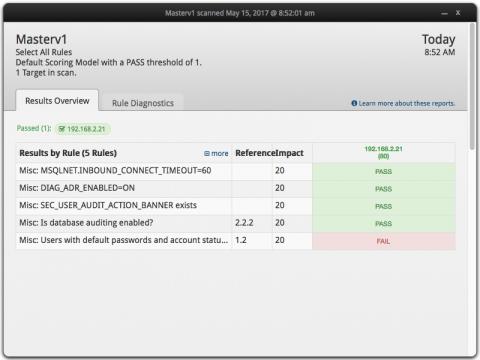
With a bit of experimentation (and great customer service from Joval), I was able to quickly prove I could develop OVAL content for automated SCAP scanning of Oracle databases, either for standard database security checks or for Oracle E-Business and/or PeopleSoft configurations. One key concern with the proof-of-concept is that connection string hardcodes the user name and password. The hardcoding is certainly a security issue, but JOVAL (as well as OpenSCAP) offers python bindings. The screen shot below is a single OVAL scan that included two SQL checks as well as checks against content in the sqlnet.ora file using the OVAL probe: textfilecontent54_test.
My OVAL definition is referenced below. I am providing it as an example for others. The key points you will know is for the JOVAL connection string for Oracle:
Engine: oracle
Version values: 11.2.0, 11.1.0, 10.2.0, 10.1.0, 9.2.0, 9.0.1
Connection string (do not use JDBC syntax): user=<username>;password=<password>;SID=<instance name>
If you want to replicate the proof-of-concept:
- Download a trial version of Joval Professional.
- Run a scan of your local laptop
- Run a remote scan of Linux server running your Oracle RDBMS
- Edit sample benchmark file (here) for your database
- Upload the edited sample benchmark into Joval
- Run the sample benchmark scan
Having proven I can use OVAL to write Oracle and ERP audit checks, I will spend a bit more time expanding the POC. I am also interested in automation options for Joval and OpenSCAP exports to a NoSQL database such as MongoDB using the Asset Reporting Format (ARF) (https://scap.nist.gov/specifications/arf/). Both Joval and OpenScap have standard functionality to export results using ARF.
If you have any questions, please contact us at info@integrigy.com
-Michael Miller, CISSP-ISSMP, CCSP, CCSK
ReferencesSample Oracle OVAL benchmark definition: SCAP OVAL Example Check for Oracle
SCAP
NIST SCAP site: https://scap.nist.gov/
SCAP content: https://nvd.nist.gov/ncp/repository?scap
Oracle Linux Security Guide – Using OpenSCAP: https://docs.oracle.com/cd/E37670_01/E36387/html/ol-scap-sec.html
Great summary of SCAP: https://energy.gov/sites/prod/files/cioprod/documents/Technical_Introduction_to_SCAP_-_Charles_Schmidt.pdf
OVAL
Writing OVAL content https://oval.mitre.org/documents/docs-07/Writing_an_OVAL_Definition.pdf
OVAL tutorial https://nvd.nist.gov/scap/docs/conference%20presentations/workshops/OVAL%20Tutorial%202%20-%20%20Definitions.pdf
Oracle E-Business Suite APPS_NE Security Risks
The most recent version of the Oracle E-Business Suite, Release 12.2, introduces on-line patching to reduce downtime requirements. This new technical functionality is based on Edition-based redefinition provided by the Oracle 11gR2 database. For the E-Business Suite to make use of Editioning, Oracle has added a new schema to the ‘APPS’ family – the APPS_NE schema.
The APPS_NE schema is the owner of those objects previously owned by APPS that cannot be Editioned or in other words; the APPS_NEW is the APPS schema for the non-editioned database objects.
There are several security implications with regard to APPS_NE:
- The same password must be shared among APPLSYS, APPS, and APPS_NE. The default password for APPS_NE is 'APPS.'
- APPS_NE has similar elevated system privileges to APPS (e.g. SELECT ANY TABLE), but is not identical. See the listing below for the 56 privileges granted to APPS_NE.
- APPS_NE must be logged, audited and monitored APPS_NE as you do APPS. APPS_NE needs to be added to your audit scripts and procedures as well as monitoring solutions
The following lists summarize the system privilege differences between APPS and APPS_NE
ALTER ANY PROCEDUREALTER DATABASEANALYZE ANY DICTIONARYCHANGE NOTIFICATIONCREATE ANY DIRECTORYCREATE ANY EDITIONCREATE ANY PROCEDURECREATE EXTERNAL JOBCREATE JOBCREATE PUBLIC DATABASE LINKCREATE PUBLIC SYNONYMDEQUEUE ANY QUEUEDROP ANY EDITIONDROP ANY PROCEDUREDROP PUBLIC SYNONYMENQUEUE ANY QUEUEEXECUTE ANY TYPEMANAGE ANY QUEUE
ALTER ANY CLUSTERALTER ANY INDEXALTER ANY MATERIALIZED VIEWALTER ANY OUTLINEALTER ANY ROLEALTER ANY SEQUENCEALTER ANY TABLEALTER ANY TRIGGERALTER ANY TYPEALTER SESSIONALTER SYSTEMANALYZE ANYCOMMENT ANY TABLECREATE ANY CLUSTERCREATE ANY CONTEXTCREATE ANY INDEXCREATE ANY MATERIALIZED VIEWCREATE ANY OUTLINECREATE ANY SEQUENCECREATE ANY SYNONYMCREATE ANY TABLECREATE ANY TRIGGERCREATE ANY TYPECREATE ANY VIEWCREATE DATABASE LINKCREATE MATERIALIZED VIEWCREATE PROCEDURECREATE ROLECREATE SEQUENCECREATE SESSIONCREATE SYNONYMCREATE TRIGGERCREATE TYPECREATE VIEWDELETE ANY TABLEDROP ANY CLUSTERDROP ANY CONTEXTDROP ANY INDEXDROP ANY MATERIALIZED VIEWDROP ANY OUTLINEDROP ANY ROLEDROP ANY SEQUENCEDROP ANY SYNONYMDROP ANY TABLEDROP ANY TRIGGERDROP ANY TYPEDROP ANY VIEWEXECUTE ANY PROCEDUREGLOBAL QUERY REWRITEGRANT ANY ROLEINSERT ANY TABLELOCK ANY TABLESELECT ANY SEQUENCESELECT ANY TABLEUNLIMITED TABLESPACEUPDATE ANY TABLE
If you have any questions, please contact us at info@integrigy.com
-Michael Miller, CISSP-ISSMP, CCSP, CCSK
References- Oracle E-Business Suite APPLSYS, APPS and APPS_NE
- Integrigy Webinar New Security Features in Oracle E-Business Suite 12.2
Recommended Approach for Oracle E-Business Suite 12.2 Mobile and Web Services Security
This is the eleventh and final posting in a blog series summarizing the new Oracle E-Business Suite 12.2 Mobile and web services functionality and recommendations for securing them.
Deploying Internet-based Oracle E-Business Suite web services requires proper configuration of the URL Firewall, both the url_fw.conf and url_fw_ws.conf and the use of a WAF – ideally the Oracle API Gateway. This recommendation applies equally to all whose only use of web services is the Oracle Supplier Network (OSN). One opening of the attack surface exposed to the Internet exposes the entire Oracle E-Business Suite.

For Mobile and Smartphone applications, due to the overall complexity and additional license requirements, it is recommended to continue using VPN for deployment instead of using an External Node.

If you have any questions, please contact us at info@integrigy.com
-Michael Miller, CISSP-ISSMP, CCSP, CCSK
Reference- Oracle E-Business Suite Mobile and Web Services Security - Integrigy Whitepaper
- Oracle E-Business Suite Mobile and Web Services Security - Integrigy Webinar
- Oracle E-Business Suite Release 12.2 Configuration in a DMZ (Note 1375670.1)
Oracle E-Business Suite APPLSYS, APPS and APPS_NE
The evolution of the Oracle E-Business Suite since its inception in the late 1980s has gone through many significant changes. For example, I can personally remember in the late 1990s upgrading clients to release 10.5 of the E-Business Suite with the big change being the introduction of the APPS schema.
The introduction of the APPS schema greatly simplified the technical interdependencies of the then 40+ applications of Release 10.5 of the E-Business Suite. The most recent version of the Oracle E-Business Suite, Release 12.2, with 200+ modules, introduces on-line patching to reduce downtime requirements. This new technical functionality is based on Edition-based Redefinition provided by the Oracle 11gR2 database. For the E-Business Suite to make use of Editioning, Oracle has added a new schema to the ‘APPS’ family – the APPS_NE schema.
The APPS_NE schema is the owner of those objects previously owned by APPS that cannot be Editioned or in other words; the APPS_NE is the APPS schema for the non-editioned APPS foundation database objects. APPS_NE has similar elevated system privileges to APPS (e.g. SELECT ANY TABLE), but is not identical. The same password must be shared among APPLSYS, APPS, and APPS_NE. The default password for APPS_NE is 'APPS.'
--This SQL gives a high-level summary of the difference between APPS and APPS_NESELECT OWNER, OBJECT_TYPE, COUNT(*)FROM DBA_OBJECTSWHERE OWNER = 'APPS_NE'GROUP BY OWNER, OBJECT_TYPEUNIONSELECT OWNER, OBJECT_TYPE, COUNT(*)FROM DBA_OBJECTSWHERE OWNER = 'APPS'GROUP BY OWNER,OBJECT_TYPEORDER BY 1,3 DESC;Oracle E-Business Suite ‘APPS’ Schemas
Schema
Description
APPS
Introduced with 10.5 of the E-Business Suite, APPS, owns all of the applications code in the database and has access all data in the Oracle E-Business Suite. All end-user connections as well connect as APPS after being authenticated using the APPLSYSPUB schema. The APPS schema must have same password as APPLSYS and APPS_NE schemas.
APPSLSYS
Owns the foundation objects (AD_* and FND_* tables) of the E-Business Suite used to define users and menus etc…. The APPLSYS schema must have same password as APPS and APPS_NE.
APPS_NE
New with 12.2, the APPS_NE schema is the Non-Editioned runtime ‘APPS’ user for the E-Business Suite. The APPS_NE schema must have same password as APPLSYS and APPS schemas.
APPS_MRC
APPS_MRC was created to support functionality for multiple reporting currencies (MRC). This schema has been obsolete since 11.5.10 and is no longer used. Its default was APPS_MRC, but country code suffixes were added (e.g. APPS_UK, APPS_JP). APPS_MRC is dropped by the upgrade to 11.5.10 and should not exist in R12 instances.
If you have any questions, please contact us at info@integrigy.com
-Michael Miller, CISSP-ISSMP, CCSP, CCSK
References- Integrigy Webinar New Security Features in Oracle E-Business Suite 12.2
-
Steps to change the APPS, APPLSYS, and APPS_NE password using FNDCPASS or AFPASSWD for EBS 12.2 (Doc ID 1674462.1) https://support.oracle.com/rs?type=doc&id=1674462.1
-
Developing and Deploying Customizations in Oracle E-Business Suite Release 12.2 (Doc ID 1577661.1) https://support.oracle.com/rs?type=doc&id=1577661.1
-
Oracle E-Business Suite Security Guide Release 12.2 (Part Number E22952-15) https://docs.oracle.com/cd/E26401_01/doc.122/e22952/T156458T659606.htm
Oracle E-Business Suite 12.2 Mobile Application Security
This is the tenth posting in a blog series summarizing the new Oracle E-Business Suite 12.2 Mobile and web services functionality and recommendations for securing them.
Oracle Corporation has been building out Mobile and Smartphone applications for the Oracle E-Business Suite for a number of releases. Before release 12.2.5, this functionality was designed only for deployment through a corporate VPN, not through an Oracle E-Business Suite external node over the Internet (e.g. a server in DMZ).
With release, 12.2.5 external node deployment for Mobile applications is now an option. 12.2.5 bundles Oracle Mobile v4 and uses the E-Business Suite's WebLogic server. Specifically, 12.2.5 deploys the Oracle Mobile v4 REST services through the OAFM WebLogic application. In other words, with 12.2.5, Smartphone applications can now be Internet deployed without a need for a separate WebLogic Server; no need for a SOA Server or a separate WebLogic server.

Oracle Mobile Using Native EBS REST
To secure version 12.2.5 Oracle E-Business Suite Mobile applications, Oracle Mobile Security Services (OMSS) is used. Check with your Oracle sales representative if OMSS is separately licensed or not. OMSS provides critical URL shortening as well as white/blacklisting and other functionality specific to deploying Oracle Mobile applications. OMSS must be properly configured and is placed in front of OAFM.

OMSS in-line before OAFM
If you have any questions, please contact us at info@integrigy.com
-Michael Miller, CISSP-ISSMP, CCSP, CCSK
References- Oracle E-Business Suite Mobile and Web Services Security - Integrigy Whitepaper
- Oracle E-Business Suite Mobile and Web Services Security - Integrigy Webinar
- Oracle E-Business Suite Release 12.2 Configuration in a DMZ (Note 1375670.1)
Oracle Unified Auditing Performance Issues and 12.2 Improvements
For those of you using and/or considering Unified Auditing, in case you might have missed, Oracle has made significant changes to Unified Auditing in 12.2. Unified Auditing, new in Oracle 12c, represents a complete rewrite of how native database auditing works - see the links below for Integrigy research on Unified Auditing.
With Oracle 12.1, when using Unified Auditing, reads of the UNIFIED_AUDIT_TRAIL view were not performant. With Oracle 12.2, a new relational partitioned table (AUDSYS.AUD$UNIFIED) is created to solve the performance issue, and a patch (22782757) has been issued to backport the fix to 12.1.
For 12.1 clients using Unified Auditing, the patch and/or the workaround should be a high priority consideration.
Thank you to Mark Dietrich for pointing out the 12.1 patch.
If you have any questions, please contact us at info@integrigy.com
-Michael Miller, CISSP-ISSMP, CCSP, CCSK
References- Oracle Support Note 2063340.1 (Performance Issues While Monitoring the Unified Audit Trail) https://support.oracle.com/rs?type=doc&id=2063340.1
- Integrigy Whitepaper: Oracle 12c Unified Auditing
- Integrigy Webinar & Presebntation: Oracle 12c Unified Auditing Webinar
- Integrigy Audit Framework Whitepaper: Integrigy Guide to Database Auditing and Logging
- Mark Dietrich's Blog: https://mikedietrichde.com/2017/04/19/unified-auditing-performance-improvements-in-oracle-12-1-0-2/
Oracle E-Business Suite 12.2 Web Services Security for Oracle Supplier Network
This is the ninth posting in a blog series summarizing the new Oracle E-Business Suite 12.2 Mobile and web services functionality and recommendations for securing them.
The most common use of web services with the Oracle E-Business Suite is the Oracle Suppler Network (OSN). Do not confuse OSN with the Oracle Social Network (also referred to as OSN) or when configuring OSN, do not confuse the Oracle Transport Agent (OXTA) web services with Oracle Training Administration (OTA) web services.
To use OSN, you must configure the both the url_fw.conf and url_fw_ws.conf file to open traffic for the XML Gateway to consume OXTA web services. The OSN documentation in places confuses OTXA and OTA. The risk is that in the url_fw_ws.conf there are services for both the Oracle Training Administration (OTA) module as well as for the OXTA. Unless both are being used, be careful to open only the correct services.
It should also be noted that while OSN uses web services, as of 12.2.5, OSN’s web services are NOT shown as deployed in the ISG repository. This is because OSN’s functionality is built into the Oracle E-Business Suite’s core functionality.
It is very important to note that while using OSN with trading partners over the Internet requires opening the E-Business Suite to the Internet. Unfortunately, it is not clearly stated that a WAF, ideally the API Gateway, should be used to protect OSN. Even if OSN is the only web service being used, a WAF is still required to guard the attack surface.
Lastly, the passwords used for the various OSN accounts (defined within the OSN GUI forms) need to be complex and regularly rotated. Many clients forget about these accounts.
If you have any questions, please contact us at info@integrigy.com
-Michael Miller, CISSP-ISSMP, CCSP, CCSK
References- Oracle E-Business Suite Mobile and Web Services Security - Integrigy Whitepaper
- Oracle E-Business Suite Mobile and Web Services Security - Integrigy Webinar
- Oracle E-Business Suite Release 12.2 Configuration in a DMZ (Note 1375670.1)
Guide to PeopleSoft Logging and Auditing - Revised Whitepaper
After discussions at Collaborate2017 with several PeopleSoft architects we have revised our Guide to PeopleSoft Auditing. The key change is the recommendation NOT to use PeopleSoft’s native database auditing and to instead use Oracle Fine Grained Auditing (FGA). FGA comes free with the Enterprise Edition of the Oracle RDBMS and, not only is it easier to implement, FGA does not have the performance impact of PeopleSoft’s native auditing.
If you have questions, please contact us at info@integrigy.com
-Michael Miller, CISSP-ISSMP
References

